CISO/IT Security
Efficient yet powerful identity lifecycle and governance management
Why Fastpath?
Business leaders have a complex set of security and compliance needs. Fastpath provides a simple, cost-effective solution to manage access control and identity lifecycle, helping organizations orchestrate all aspects of their identity and access security from one platform. We automate compliant provisioning to continuously ensure that the right people have the right access at the right time. Plus, we integrate with leading GRC tools like AuditBoard, Workiva, ServiceNow, Jira and Active Directory so you can put us at the center of your GRC program.

Automate Identity Workflows
Fastpath lets users request access without the need for IT intervention. We’ve streamlined user setup, approvals, and audit trails to streamline workloads and reduce costs. Automate access as users join, move within, or leave the organization so you can easily manage all identities.

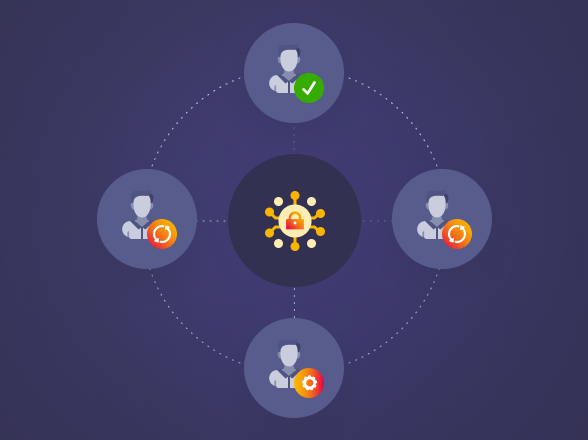
Establish Zero Trust
Fastpath enables you to seamlessly orchestrate access control management and identity governance administration across all business applications. Move toward a zero trust strategy and ensure users are granted only the access they need. Fastpath gives you a single view of user access across all systems, allowing total confidence in security and audit reporting.
Prevent Separation of Duties Violations
The ability to manage access and identify Separation of Duties (SoD) risk across a whole enterprise has become increasingly important. Fastpath empowers organizations to identify, mitigate and remediate SoD violations quickly, analyzing access in business software by user or role down to the lowest security level, reporting on conflicts across applications so you can minimize risk, reduce fraud and remove unsafe access combinations.

Maintain and Secure Controls
Securing multiple applications is complex but critical. As your business grows and threats evolve, it becomes increasingly important to enforce access policies. Fastpath enables you to design, monitor and manage all controls from one platform, ensuring consistency across applications, geographies, and business units.

